Reliable Connection
Sophos SSL VPN Client for Windows
1
Why Sophos VPN Is the Best Choice for Secure Connectivity
When it comes to protecting your remote workforce and ensuring seamless access to critical business resources, not all VPN solutions are created equal. The right solution must balance enterprise-grade security with user-friendly operation, providing IT administrators with the control they need while offering end-users a frictionless experience. Our solution delivers on all fronts, combining decades of security expertise with modern architectural principles to create a VPN platform that organizations can truly rely on.
The Sophos VPN Client stands apart from competing solutions through its deep integration with comprehensive security ecosystems. Unlike standalone VPN tools that operate in isolation, our solution was built from the ground up to work in harmony with endpoint protection, threat intelligence, and access control systems. This means that when a user establishes a connection, the device itself is continuously evaluated for compliance—checking for active security software, up-to-date patches, and the absence of malicious activity before permitting access to sensitive resources. This layered approach to security ensures that even if credentials are compromised, the overall network remains protected. Furthermore, the administrative experience is designed for efficiency, allowing IT teams to deploy configurations across hundreds or thousands of endpoints from a single console, dramatically reducing the operational overhead traditionally associated with managing remote access infrastructure.
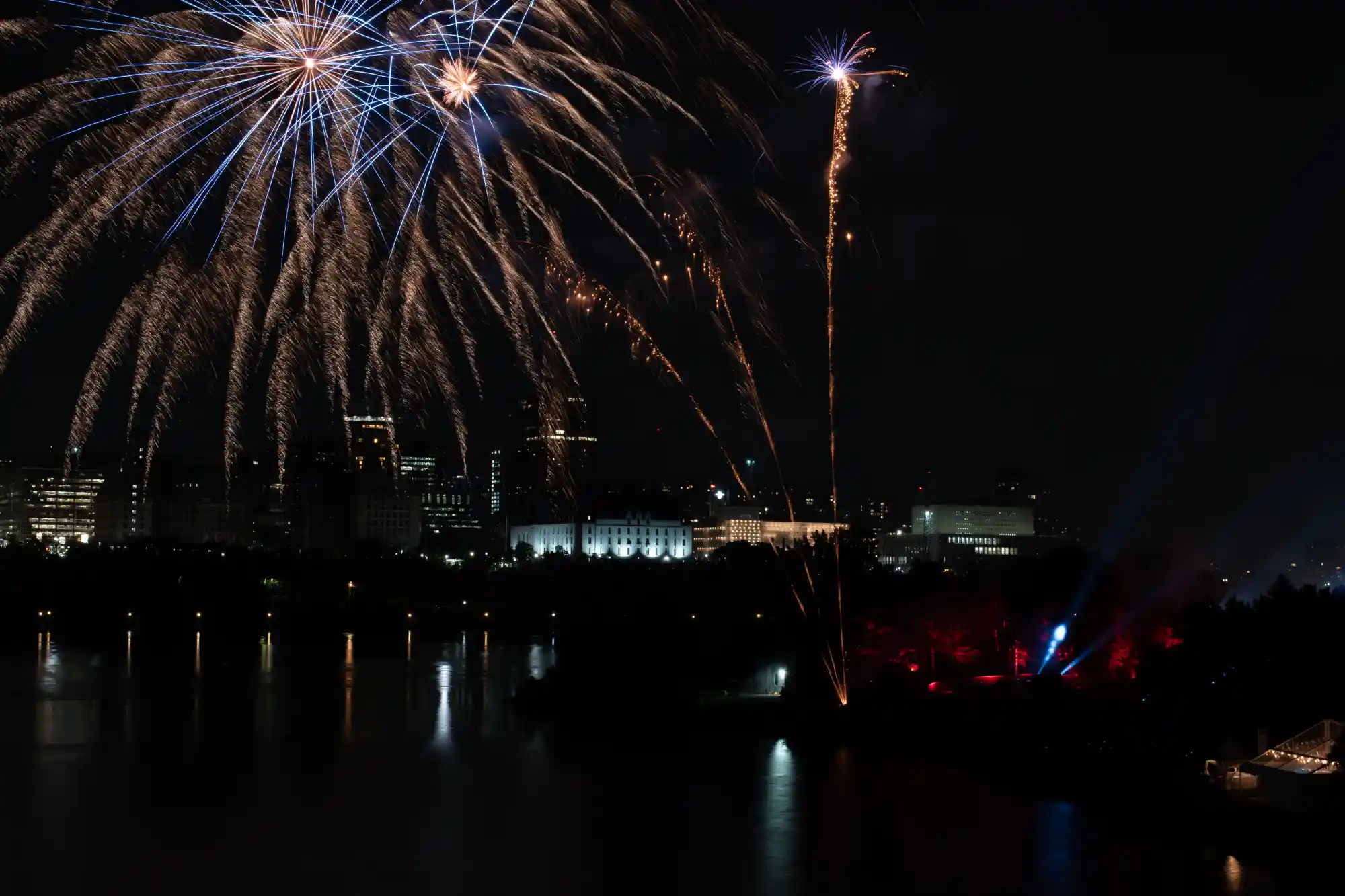
For organizations seeking a reliable solution, the ability to download Sophos VPN Client represents the first step toward establishing a secure, scalable remote access framework. The installation and configuration process has been carefully refined to eliminate complexity, enabling rapid deployment across diverse operating environments. Once deployed, users benefit from a clean, intuitive interface that makes connecting to corporate resources as simple as a single click. Behind this simplicity lies sophisticated technology: support for multiple VPN protocols ensures compatibility with any network environment, while intelligent connection logic automatically selects the optimal configuration based on the user’s location and network conditions. Whether employees are working from home offices, traveling internationally, or connecting from co-working spaces, the connection remains stable, secure, and fast. This reliability translates directly into productivity, allowing teams to focus on their work rather than troubleshooting connectivity issues. For IT administrators, centralized management capabilities provide full visibility into connection status, usage patterns, and potential security events, enabling proactive responses before minor issues escalate into major incidents. The sophos ssl vpn client architecture specifically addresses the challenges of modern network environments, utilizing the ubiquitous HTTPS port to ensure connectivity even through restrictive firewalls and captive portals that commonly block traditional VPN protocols, making it an ideal choice for organizations with mobile workforces.
2
Enterprise-Grade Security Delivered with Simplicity Sophos
In today’s threat landscape, organizations cannot afford to compromise between security and usability. The ideal remote access solution must provide robust protection against sophisticated cyber threats while remaining simple enough for everyday users to operate without constant IT intervention. Our solution achieves this delicate balance through thoughtful design, powerful automation, and a commitment to security excellence that permeates every layer of the software architecture.
What truly distinguishes this solution is its unified approach to endpoint and network security. Traditional VPN tools simply establish a tunnel and step aside, offering no visibility into the health of the connecting device. Our software takes a fundamentally different approach by maintaining continuous communication with the broader security infrastructure. Before a connection is ever established, the device undergoes a thorough health assessment. Is antivirus software active and up to date? Are critical security patches installed? Is there any evidence of compromise? Only when these conditions are satisfied does the connection proceed. This pre-connection validation prevents compromised or non-compliant devices from becoming entry points for attackers. But the protection does not stop there. Throughout the duration of the session, ongoing monitoring ensures that if a device becomes compromised after connection—perhaps through a drive-by download or phishing attack—access can be terminated immediately, isolating the threat before it can spread laterally across the network. This proactive, continuous assessment model represents a significant evolution beyond traditional VPN architectures.
The experience for IT administrators has been equally transformed. Managing remote access across a distributed organization once required tedious manual configuration on each individual device, a process that was time-consuming, error-prone, and difficult to scale. Our centralized management capabilities eliminate these challenges entirely. Administrators can define security policies, configure connection profiles, and deploy updates to thousands of endpoints simultaneously from a single web-based console. Real-time dashboards provide instant visibility into who is connected, from where, and what resources they are accessing. Detailed logging and reporting capabilities support compliance audits and security investigations, while automated alerting ensures that administrators are notified immediately of unusual activity or potential threats. This operational efficiency allows IT teams to focus on strategic initiatives rather than being consumed by routine maintenance tasks. For end-users, the experience is equally streamlined. The software maintains persistent, secure connectivity without requiring constant manual intervention, and when issues do arise, built-in diagnostic tools provide clear guidance that empowers users to resolve simple problems without escalating to the help desk. The result is a solution that reduces friction for everyone involved while maintaining uncompromising security standards.

Director of IT Infrastructure
Michael Chen
When our organization transitioned to a fully distributed workforce, we knew we needed a VPN solution that could scale without compromising security. After evaluating several options, we chose Sophos VPN, and it has exceeded our expectations in every way. The deployment process was remarkably smooth—our IT team had profiles configured and pushed out to over three hundred employees within a matter of days. What impressed me most was the seamless integration with our existing security infrastructure. The pre-connection health checks give me confidence that only compliant devices are accessing our network, and the centralized management console provides the visibility I need to monitor connections and respond to potential threats in real time.
Beyond the technical capabilities, the user experience with Sophos VPN has been exceptional. Our employees, many of whom are non-technical, found the software intuitive from day one. No more help desk tickets about failed connections or confusing error messages. The stability is outstanding—even team members working from locations with challenging internet connectivity report consistent, reliable performance. This combination of robust security and effortless usability is rare in the enterprise software space, and Sophos VPN has made a tangible difference in our team’s productivity. I confidently recommend this solution to any organization serious about securing their remote workforce without sacrificing operational efficiency.
250,000+
Downloads Worldwide
Trusted by users across six continents
15,000+
Active Organizations
From small businesses to global enterprises
99.9%
Connection Reliability
Engineered for consistent, stable performance
24/7
Technical Support
Expert assistance when you need it most
3
How We Compare: The Clear Choice for Secure Remote Access
Selecting the right VPN solution requires careful evaluation of security capabilities, management complexity, and total cost of ownership. While many alternatives offer basic connectivity features, few deliver the comprehensive protection, centralized control, and seamless user experience that modern organizations demand. Below is an honest comparison of how our solution stacks up against other leading options in the market. The differences speak for themselves.
| Feature | Sophos VPN | Competitor A | Competitor B |
|---|---|---|---|
| Endpoint Health Check | ✅ Pre-connection compliance verification | ❌ Not available | ⚠️ Limited basic checks |
| Centralized Management | ✅ Single console for full fleet control | ⚠️ Requires multiple tools | ✅ Available but complex |
| Multi-Protocol Support | ✅ IPsec, SSL/TLS, OpenVPN | ⚠️ Limited protocol options | ✅ Multiple protocols |
| Zero Trust Integration | ✅ Full integration with security ecosystem | ❌ No integration | ⚠️ Partial integration |
| User Experience | ✅ Intuitive, minimal training required | ⚠️ Steep learning curve | ✅ Moderate usability |
| Multi-Factor Authentication | ✅ Native MFA support | ⚠️ Requires third-party | ✅ Built-in support |
| Automated Provisioning | ✅ One-click deployment at scale | ❌ Manual configuration | ⚠️ Complex setup |
| Real-Time Visibility | ✅ Live dashboards and alerts | ⚠️ Limited reporting | ✅ Comprehensive logs |
| Cross-Platform Support | ✅ Windows, macOS, Linux | ⚠️ Limited OS coverage | ✅ Multiple platforms |
| Deployment Time | ✅ Minutes for thousands of users | ❌ Days or weeks | ⚠️ Hours with expertise |
| Support | ✅ 24/7 expert assistance | ⚠️ Business hours only | ✅ 24/7 available |
| Pricing Model | ✅ Transparent, predictable | ⚠️ Hidden fees common | ✅ Competitive but complex |
4
Frequently Asked Questions
Have questions about implementing and using our VPN solution? We’ve compiled answers to the most common inquiries to help you better understand what we offer and how it can benefit your organization. If you need additional information, our support team is always ready to assist.
Is the Sophos VPN solution difficult to deploy across a large organization?
Not at all. Our centralized management capabilities allow IT administrators to configure connection profiles, define security policies, and deploy them to hundreds or thousands of endpoints from a single console. The process takes minutes rather than days, and automated provisioning eliminates the need for manual configuration on each individual device.
What security protocols does the software support?
Our solution supports multiple industry-standard protocols including IPsec, SSL/TLS, and OpenVPN. This flexibility ensures compatibility with virtually any network environment while allowing administrators to choose the optimal protocol based on their specific security requirements and network conditions.
Can the software integrate with our existing security infrastructure?
Absolutely. Our VPN solution is designed to work seamlessly with broader security ecosystems, including endpoint protection platforms, identity providers, and multi-factor authentication systems. Pre-connection health checks verify device compliance before granting access, creating a unified security posture rather than operating in isolation.
Is the software suitable for organizations with remote and mobile workforces?
Yes, this is exactly where our solution excels. The software is optimized for diverse network environments, automatically adapting to varying connection conditions. Whether employees are working from home offices, traveling internationally, or connecting from public Wi-Fi, they experience stable, reliable connectivity without complicated manual adjustments.